BitLocker is a data protection feature which protects a disk from being read if it is stolen, lost or inappropriately decommissioned.
Trusted Platform Module
BitLocker provides the most protection when used with a Trusted Platform Module (TPM) version 1.2. The TPM is a hardware component installed in many newer computers by the computer manufacturers. It works with BitLocker to help protect user data and to ensure that a computer has not been tampered with while the system was offline.
System integrity verification
BitLocker can use a TPM to verify the integrity of early boot components and boot configuration data. This helps ensure that BitLocker makes the encrypted drive accessible only if those components have not been tampered with and the encrypted drive is located in the original computer.
BitLocker helps ensure the integrity of the start-up process by taking the following actions:
- Provide a method to check that early boot file integrity has been maintained, and help ensure that there has been no adversarial modification of those files, such as with boot sector viruses or rootkits.
- Enhance protection to mitigate offline software-based attacks. Any alternative software that might start the system does not have access to the decryption keys for the Windows operating system drive.
- Lock the system when it is tampered with. If any monitored files have been tampered with, the system does not start. This alerts the user to the tampering, because the system fails to start as usual. In the event that system lockout occurs, BitLocker offers a simple recovery process.
Suspending BitLocker
BitLocker drive encryption needs to be suspended prior to making any of the following changes:
- OS Upgrade/Installing additional OS
- Hardware Change (e.g. Installing PCI cards)
- Firmware updates
- Non-Microsoft application updates that modify boot components.
BitLocker encrypted devices use the TPM chip to verify the integrity of early boot components and boot configuration data. This helps ensure that BitLocker makes the encrypted drive accessible only if those components have not been tampered with and the encrypted drive is located in the original computer.
This means that if a hardware change or change in the Boot Configuration Data is detected on boot, TPM will not release the BitLocker key and the computer will not be able to boot to Windows. BitLocker therefore needs to be suspended before making any of the above changes.
Contact the ISD IT Services if you need to do this.
Recovery key
A recovery key is required when the computer cannot access the OS partition. This happens if the TPM chip cannot verify the integrity of early boot components and boot configuration data or the TPM chip is not present at all.
Such scenarios are:
- Upgrade of the system board or TPM.
- Damage to a computer that causes the user to move the BitLocker-enabled volume to a different computer with a different TPM or no TPM at all.
- Turning off, disabling, or clearing the TPM.
- Upgrading critical early boot components that causes the TPM to fail validation.
When you need to enter your recovery key, the computer – instead of booting to Windows – will show the following screen:
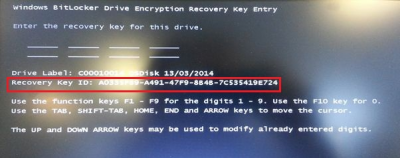
The recovery keys are stored securely in the UCL Active Directory and access is tightly controlled. If you do find yourself in a situation where a recovery key is required you should call the ISD IT Services in the first instance who will then invoke the key recovery process. The Recovery Key ID (location highlighted above) should be provided when logging the call.
 Close
Close

