Part of a reliable approach to handling confidential information is to assess the risk of information storage and transfers.
It is critical to identify and form a register of your information assets. Assets may include, as examples, completed consent forms, a database of participant questionnaire responses or transcripts from participant interviews. You can start adding to the information asset register by clicking here. The New button in the ribbon (near the top left) is for recording a new asset.
Information assets should have ownership assigned to them (which is your information asset owner), they should be reviewed regularly, for example, for retention, and they should be classified under the terms of UCL's Information Management Policy (found here), and the information classification scheme within it. By classifying information assets you are more easily able to assess the risk of storing and transferring them. In order to judge risk you also need to state how the asset is protected when it is stored and transferred, i.e. irrespective of how it is stored or transferred, through encryption, pseudonymisation or anonymisation (or none of these, where it is not possible), and on what type of storage and the type of transfers it will be subject to.
Human nature tends for us to exaggerate short term, more uncommon risks and overlook the most common risks and the longer term risks, so the idea of this risk assessment process is to capture risks uniformly and objectively.
If you are working on a research project after registering with the ISD Information Governance service you have to record that the information risk procedure has been completed under Information Risk (Stage 3) on the Information Governance Advisory SharePoint, as part of the required evidence.
More detailed guidance is found below:
Purpose
The purpose of the Information Risk procedure is to inform the design of a project so that privacy for participants is maximised. Research project information asset owners or administrators are required to carry out this procedure at the earliest possible juncture so that the project is informed of the best possible choices it can make around technology and services for processing highly confidential information.
Before completing the Information Risk procedure
Users should assemble the views of senior managers, study co-ordinators, staff and, where possible, the individuals affected. All of these viewpoints should be considered in assessing the privacy requirements of the project. However, all legislation, regulations, contracts and UCL policies, procedures and guidance should be adhered to irrespective of whether the risk assessment indicates a low or a high risk. It is best if everyone involved in carrying out the assessment has been through training in information governance beforehand.
The Information Asset register
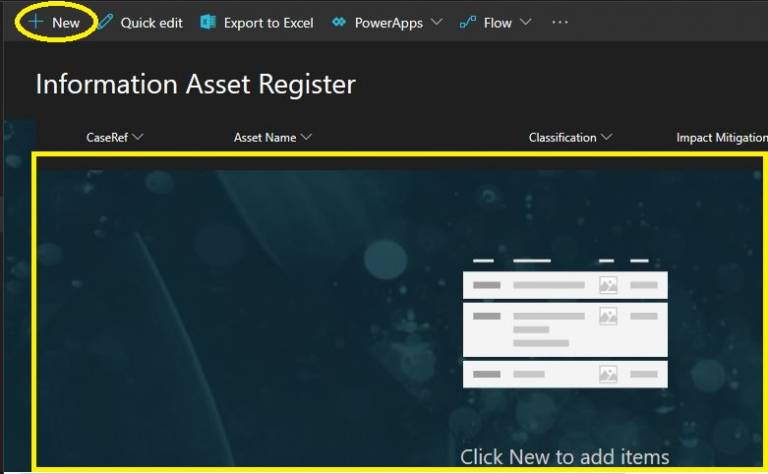
Click on 'New' to begin creating assets
Each row in the asset register should contain one data set that is held by the project. If two or more data sets are combined then this will result in three or more information assets until such time as the 2+ original assets are destroyed. If you record that the asset is stored on more than one type of media or service then the system will replicate your asset to each of those types of media or service in the asset register automatically.
Users are required to consider UCL guidance on anonymisation/pseudonymisation and encryption when describing assets as protected in this way. Assets need to be captured in all of their actual locations and forms, separately. For example, users should record all: anonymised versions, encrypted files that contain one or more assets, paper and electronic assets etc.
To create an asset and add it to the register, the user clicks 'New' and on doing so the 'Asset Details' form should appear on the right.
The system will inform you of a risk rating for each asset which will be related to both its impact (by its classification and any mitigation applied to the data itself) and the likelihood of a breach (as assessed per storage media or service by UCL).
Once the assessment has been carried out
Risks identified in the assessment should be considered and any mitigation strategies agreed in liaison with the Information Governance Advisory Service (infogov@ucl.ac.uk). The information asset owner or information asset administrator will need to provide confirmation that the risks are acceptable. However, any ‘red risks’ of 18 or higher do require improvement steps to be implemented and should be alerted to the information asset owner and the Information Governance Advisory Service for advice. If additional measures cannot be found to mitigate these risks within the process (by amending the asset register and the underlying process owned by the research project), then the Senior Information Risk Owner within the UCL School of Life and Medical Sciences will be asked to either accept or reject the activity based on the risk.
If you have reached a satisfactory conclusion on the above then you need to confirm all aspects of the process have been completed using the Information Risk form for 'Stage 3' to be completed.
 Close
Close

